Microsoft Monitoring Agent DSC resource updated to enable AD and management groups configuration
A couple of weeks ago, I had announced a custom DSC resource module to install and configure Microsoft Monitoring Agent that is required to configure Azure Operational Insights. It was released with only Operational Insights enablement. Today I pushed a new version of this module to include management group configuration for connecting to on-premises Operations Manager deployment and Active Directory integration. With these two new resources, the cMMAgent DSC resource module is complete and contains six resources.
Microsoft Monitoring Agent (cMMAgent) DSC resource module contains the following resources.
- cMMAgentInstall is used to install Microsoft Monitoring Agent.
- cMMAgentProxyName is used to add or remove the proxy URL for the Microsoft Monitoring Agent configuration.
- cMMAgentProxyCredential is used to add, modify, or remove the credentials that need to be used to authenticate to a proxy configured using cMMAgentProxyName resource.
- cMMAgentOpInsights is used to enable or disable Azure Operational Insights within the Microsoft Monitoring Agent. This can also be used to update the WorkspaceID and WorkspaceKey for connecting to Azure Operational Insights.
- cMMAgentAD is used to enable or disable Active Directory integration for the Microsoft Management Agent. By enabling AD integration, you can assign agent-managed computers to management groups.
- cMMAgentManagementGroups DSC resource can be used to add or remove management groups. You can use this resource to update the action account credentials for the management agent service.
Along with the two new DSC resources there are a couple of breaking changes. I renamed UpdateWorkspace property in cMMAgentOpInsights resource and UpdateCredential property of cMMAgentProxyCredential resource to Force. This decision was taken to ensure that the resource design is inline with the recommended DSC best practices and patterns.
You can take a look at the readme on Github for a complete overview of each resource in the cMMAgent DSC module. Here is an explanation of the two new resources I added today.
Using cMMAgentAD resource
The cMMAgentAD resource can be used to enable or disable Active Directory (AD) integration. With AD Directory Services integration, the agent-managed computers can be automatically assigned to the Operations Manager management groups.
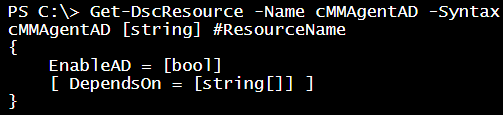
There is only one property that is EnableAD. This is a Boolean property. Setting this to True enables AD integration and disables otherwise.
cMMAgentAD MMAgentAD {
EnableAD = $true
}
{#user-content-using-cmmagentmanagementgroups-resource.anchor}Using cMMAgentManagementGroups resource
The cMMAgentManagementGroups resource enables you to add or remove Operations Manager management groups from the Microsoft Monitoring Agent configuration. Additionally, you can configure action account credentials for the agent service.
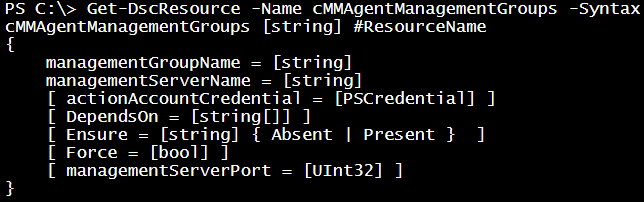
The ManagementGroupName and ManagementServerName properties are mandatory. The ManagementServerPort is optional and set to 5723, by default. This property need not be changed unless your Operations Manager implementation is customized.
cMMAgentManagementGroups MMAgentManagementGrup {
ManagementGroupName = 'SCMgmtGroup'
ManagementServerName = 'SCOM-1'
Ensure = 'Present'
}
You can specify the action account credentials for the management agent service. This needs to be a PSCredential object. So, as per the DSC best practices, you must encrypt these credentials using certificates.
cMMAgentManagementGroups MMAgentManagementGrup {
ManagementGroupName = 'SCMgmtGroup'
ManagementServerName = 'SCOM-1'
ActionAccountCredential = $Credential
Ensure = 'Present'
}
If you do not have certificate implementation in your test or development infrastructure, you can use DSC configuration data to allow plain text credentials.
$ActionAccountCredential = Get-Credential
$ConfigData = @{
AllNodes = @(
@{ NodeName = '*'; PsDscAllowPlainTextPassword = $true },
@{ NodeName = 'WMF5-1' }
)
}
Configuration MMAgentConfiguration {
Import-DscResource -ModuleName cMMAgent
Node $AllNodes.NodeName {
cMMAgentManagementGroups MMAgentManagementGrup {
ManagementGroupName = 'SCMgmtGroup'
ManagementServerName = 'SCOM-1'
ActionAccountCredential = $ActionAccountCredential
Ensure = 'Present'
}
}
}
Once you add a management group, if you need to update the action account credentials, you can use the Force property. When you set Force property to True, the action account credentials get updated. The value of Ensure property has no meaning when using the Force property. Also, when using Force, the actionAccountCredential property must be set.
$updatedActionAccountCredential = Get-Credential
$ConfigData = @{
AllNodes = @(
@{ NodeName = '*'; PsDscAllowPlainTextPassword = $true },
@{ NodeName = 'WMF5-1' }
)
}
Configuration MMAgentConfiguration {
Import-DscResource -ModuleName cMMAgent
Node $AllNodes.NodeName {
cMMAgentManagementGroups MMAgentManagementGrup {
managementGroupName = 'SCMgmtGroup'
managementServerName = 'SCOM-1'
actionAccountCredential = $updatedActionAccountCredential
Force = $true
}
}
}
This is it. So, what is next? I will publish the DSC resource modules that I am developing to PowerShell Gallery so that you can use PowerShellGet module to download them to target systems. Stay tuned.
Share on: